Now it’s very frequent, the hackers break into a merchant’s computer system and steal credit card information, which they can use to charge huge amounts worth of stuff to your account. But imagine if instead of a person’s name, card number, expiration date, and other information, the hackers just got a meaningless jumble of numbers and letters – That’s credit card tokenization in action, and it’s a key way payment systems can keep card data safe.
Tokenization is a data security feature where a sensitive data element or set is effectively replaced (“tokenized”) with a non-sensitive alternative, called a token. This renders the data completely useless to exploitation. means, Tokenization replaces sensitive card data with a jumble of letters and numbers that are useless to a hacker. Tokenization can be used to safeguard any sensitive data like PII data, medical records, banking, and credit card payments. Credit Card tokenization is the process of replacing sensitive customer details with an algorithmically generated number that is impossible to trace back to the original data or information. The result – a (credit card) token – makes it impossible for anybody to misuse sensitive information, as the tokenization algorithm ensures that the data is unable to be traced back to its original source. As an example, when a customer makes a purchase using a credit or debit card, the tokenization process takes the card number and transforms it into a mathematically irreversible token. If the credit card number or account number needs to be billed again in the future such as for recurring payment or subscription, the payment system recognizes the token associated with the card, rather than the card number itself. Credit or debit card tokenization increases trust for organizations and significantly reduces the risk of sensitive data such as cardholder data being exposed.

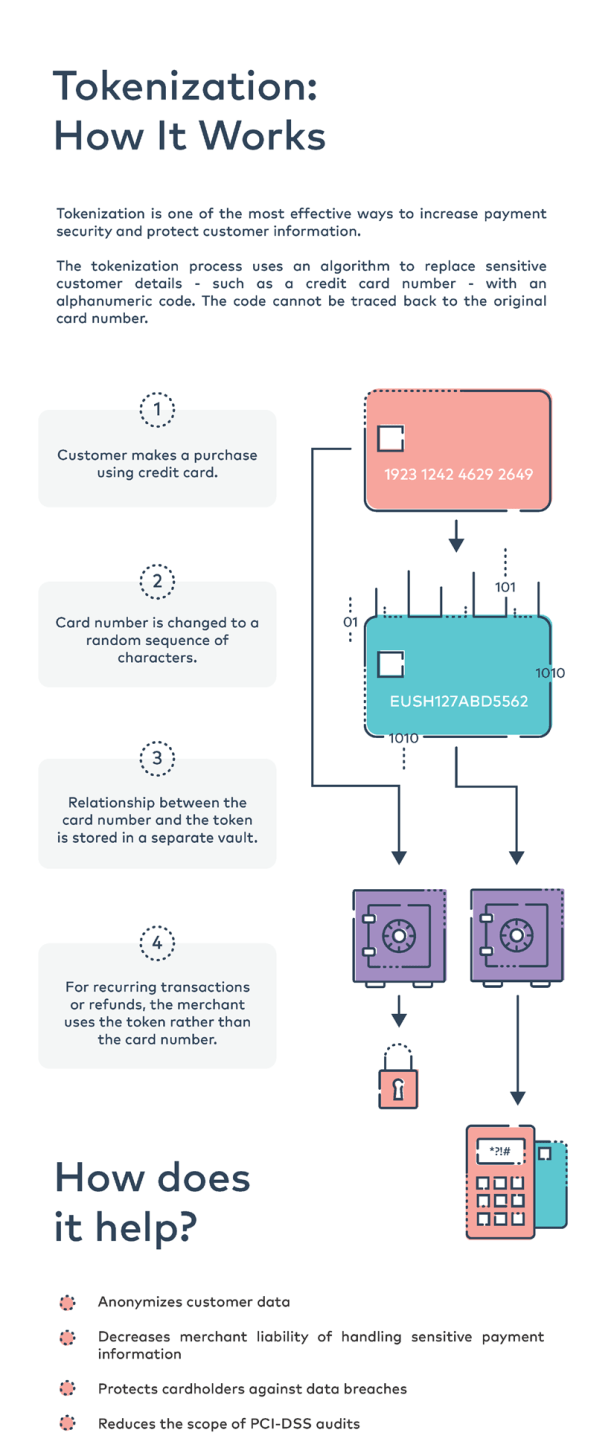
The tokenization process can take many forms, but it’s useful to consider the following possible scenarios:
1. E-commerce Payment Tokenization
- A customer makes a purchase and uses their credit card to check out (ex. 1234 4321 1234 5678).
- The card number is changed to a random sequence of characters (ex. EUSH127ABD5562).
- The relationship between the actual card number and the token is stored in a separate vault.
-
If the transaction is recurring for a monthly or another subscription or a refund is required, the merchant can simply use the token rather than needing to store the sensitive card data itself.2. Mobile Payment Tokenization
When users of Apple Pay or Android Pay add a credit card to their mobile device, each of the card numbers will be tokenized and stored on the phone. When a purchase is made, the token is used instead of the payment card itself, thus adding an extra layer of protection for the transaction.
3. App Payment Tokenization
Now days, using applications to purchase goods is becoming more common, If a user’s phone contains a token, these apps are unable to retrieve or access any credit card details. All bank details are locked down and hackers/fraudsters would be unable to commit an offense with the data available to them. Checking out to finalize a purchase is simple too as many apps are integrated to be linked directly with your stored shipping and billing information.
The decrease in data theft and fraud as a result of tokenization means businesses are less likely to incur reputational or financial damage as a result of a data breach. Customers will also feel reassured and confident in shopping with merchants who utilize a tokenization process, as this shows a strong emphasis on protecting the sensitive information of the customer. Tokenization also has additional benefits, particularly when combined with PCI-validated Point-to-Point Encryption.
Tokenization Vs. Encryption
When data is encrypted, it is coded into a hidden language, similar to tokenization. However, encryption uses a mathematical formula that is possible to reverse-engineer, meaning encrypted sequences can be deciphered and risks exposing sensitive information such as credit card data.
Conversely, tokenization turns a meaningful piece of data into a string of random characters that cannot be reversed – so if breached, no meaningful value is exposed. This is a huge benefit in the payment card industry, ensuring the highest security standard possible. The only thing a hacker would obtain is a list of token numbers which would be of no use to them. This makes credit card data unusable, adding additional layers of security.
Benefits of Tokenization:
Tokenization can provide several important benefits for securing sensitive customer data:
-
Enhanced customer assurance—tokenization offers an additional layer of security for eCommerce websites, increasing consumer trust.
-
Increased security and protection from breaches—by using tokenization, businesses do not have to capture sensitive information in their input terminals, keep it in internal databases, or transmit the data through their information systems. This safeguards businesses from security breaches.
-
Data tokenization improves medical records security—organizations can use tokenization solutions for scenarios covered under HIPAA. By substituting electronically protected health information (ePHI) and non-public personal information (NPPI) with a tokenized value, healthcare organizations can better comply with HIPAA regulations.
-
Tokenization makes credit card payments more secure—the payment card industry needs to comply with extensive standards and regulations. Tokenization solutions provide a way to protect cardholder data, such as magnetic swipe data, primary account number, and cardholder information. Companies can comply with industry standards more easily, and better protect client information.
Tokenization for Security and Compliance:
Tokenization can be approached on multiple layers of protection, including:
-
Database firewall—prevents SQL injection and similar threats, while assessing for known vulnerabilities.
-
User rights management—tracks the data movements and access of privileged users to identify excessive and unused privileges.
-
Data loss prevention (DLP)—monitors and tracks data in motion, at rest, in cloud storage, or on endpoint devices.
-
User behavior analytics—creates a baseline of data access behavior and uses machine learning to isolate and alert on abnormal and potentially dangerous activity.
-
Data discovery and classification—discloses the volume, location, and context of data on-premises and in the cloud.
-
Database activity monitoring—monitors relational databases, data warehouses, big data, and mainframes to produce real-time alerts on violations of policy.
-
Alert prioritization—using AI and machine learning technology to examine the stream of security events and prioritize the most important events.